Each month, the term “IL3” is one of the highest search queries that brings visitors to the Ascentor website, and it’s been this way for some time. In fact, a search for “IL3” on Google lists Ascentor in the 1st, 2nd and 3rd rankings. However, with the recent demise of the IS1/2 standard, there was an expectation that the search term would no longer be relevant – but our visitor numbers disagree. So, what is “IL3”, why are people still searching for it, and could there be more appropriate search options?
This article looks at the history of Impact Levels (ILs), examines how they were misused and suggests alternative search terms and phrases you may also find helpful.
Ascentor and “IL3”
Over the years, Ascentor has written a number of articles that refer to the term “IL3” – Useful tips for IL3 accreditation and IL0, IL1/2, IL3? Busting the G-Cloud Accreditation Security Jargon to name just two. All have proven to be very popular and remain amongst our most-read content – which is what sparked our curiosity about the continued interest in such a specific search term.
A bit of history
Impact Levels (ILs) were introduced into the UK Government’s risk assessment process with the publication of Information Assurance Standard No. 1 version 2.1 in 2003. They were later updated to Business Impact Levels (BILs) in version 2.2 in 2007.
Prior to version 2.1, confidentiality was king of the information risk assessment. Version 2.1 of the standard ensured that integrity and availability took more of a front seat. This meant that the three well-known pillars of information risk were each measured separately. So, one of the questions would be:
“What would the impacts be if there was a loss of confidentiality, and integrity and availability?”
For government departments, answering the confidentiality question was easy. Someone had already done all the hard work and mapped the impact assessments of losing information directly to the Protective Markings as Figure 1 shows.
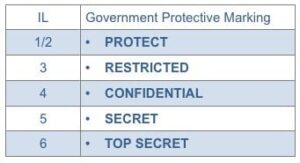
Figure 1: Mapping of ILs to Protective Markings
Great pains were taken to say that this was a one-way mapping i.e. TOP SECRET would always be IL6 but IL6 would not always mean TOP SECRET. Some analysts found this hard to get their heads around.
Think of a company like Ascentor Ltd; we have information that relates to how the company is run and future plans. In IL terms, we would equate this to IL5 because it would have a severe impact on the way we do business if that information became publicly available. However, that does not mean the information is SECRET according to the Government Protective Marking Scheme.
The same is true for integrity and availability measurements. An assessment of IL6 impact for availability did not make the system TOP SECRET. Think of an air-traffic control system. Availability and integrity are key – confidentiality takes a well-deserved break.
So, people started to refer to system security requirements in terms of ILs for Confidentiality, Integrity and Availability:
“I need an IL 3, 2, 3 system.”
“The system must be accredited to IL 4, 4, 5.”
Eventually, all pretext was dropped, and it became common for a single IL to cover a complete system “This is an IL3 system”. What that actually means is very unclear. Without knowing the sensitivity of the information and the context of the integrity and availability requirements, the ILs were used to imply a worthless statement of security requirements.
The use of impact levels as a means of conveying a security requirement is where the problem starts, particularly when it’s stated as an upfront requirement without understanding the business need behind that requirement.
Dave James, MD Ascentor Ltd
The withdrawal of the IS standard
CESG withdrew the IS1&2 standard in January 2015. The IS1&2 Technical Supplement is still available and can be used by any organisation looking for a robust risk assessment methodology. However, CESG will no longer provide updates to it. Instead, they prefer that organisations take responsibility for their own risk assessment processes, which will invariably include some level of impact assessment. The important thing is that the negative impact of a possible security event is assessed and understood in each business context.
So, there is little point in searching the Internet for information on how to accredit an IL3 system or the security controls applicable to an IL4 system because you are unlikely to find anything that is applicable to your particular system and business. Any you do find (such as those on the Ascentor website) will be specific to a particular system or framework (such as PSN or G-Cloud) where the boundaries were well-defined.
What are the alternative searches?
In addition to searching for “IL3 accreditation” or “IL5 security requirements”, also try more specific searches such as “PSN accreditation” or “security standards for a data centre”. Alternatively, searching for a “cyber security consultancy” such as Ascentor should lead you to the expertise you need to understand your security requirements.
The point is to understand the impact that a security incident will have on your business and then determine a) if you need to do anything about it or b) what it is you should do.
Simply quoting numeric impact levels is a sign that the risk is not really understood.
For further information
If you have found this article of interest, the Ascentor blog regularly carries articles about cyber security and information assurance issues. You might also like to keep in touch with Ascentor by receiving our quarterly newsletter and following us on LinkedIn and Twitter.
If you’d like to discuss how our consultants could advise on any aspect of cyber security, please contact Dave James at Ascentor.